The fundamentals of cyber security involve IP addresses and protocols and a variety of defenses from Public Key Infrastructure to digital signatures and certificates and e-tendering and procurement. Web applications, Information Technology Services (ITS), and mobile security are additional areas of focus for cyber security experts.
Running Security Audits in Today’s Complex IT World
Organizations of all sizes today are constantly under the threat of internet and mobile security threats. The main issue at hand is the privacy of business and personal data. When it is in the hands of hackers, this information can cause great harm. This brings up the need for continual security audits which are difficult to perform correctly because of the complexity of today’s networks.
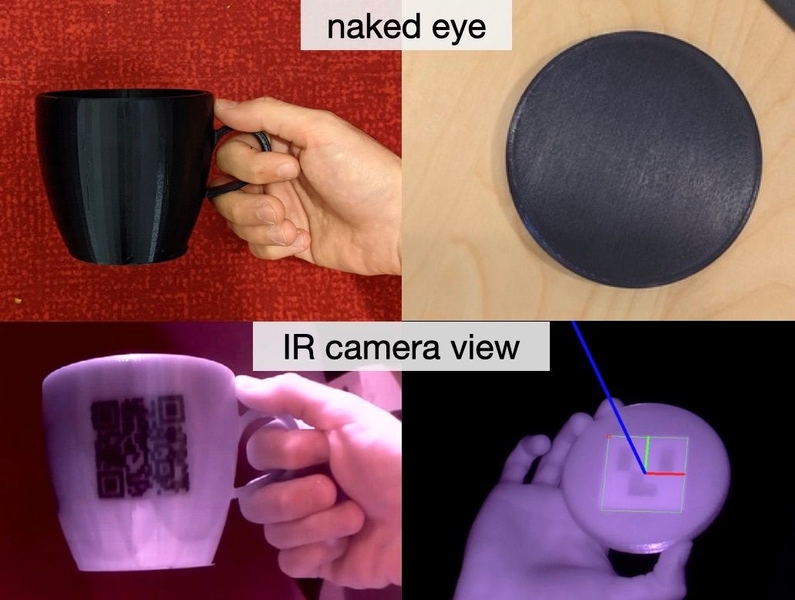
So far, most mobile devices have provided manual entry of passwords as the main security system. But manual entry is often frustrating, causing people to create extremely simple passwords that can be hacked in minutes. And creating screens that look like legitimate sites or password entry screens, AKA spoofing, is more rife than ever.
For a mobile device to be secure, the human-to-machine authentication process must be bulletproof. It would seem to be a pretty easy problem to solve, but it is far from that.
Biometric Security
One technology emerging with considerable promise in improving cyber security on mobile networks is mobile biometrics. Mobile biometrics uses complex algorithms and mobile device memory to create a higher level of security than is currently available through password-based systems.
Security companies are now offering biometric identity management solutions to companies of all sizes. The strength of the new biometric identity technology is that it can be integrated into interoperable systems.
The following video explains “Mobile Payment with Biometric Authentication.”