According to Sun Tzu in The Art of War: “It is said that if you know your enemies and know yourself, you will not be imperiled in one-hundred battles; if you do not know your enemies, but do know yourself, you will win one and lose one; if you do not know your enemies, nor yourself, you will be imperiled in every single battle.” If we were to distill Sun Tzu’s message, it would be: today’s companies don’t need more weapons, they need the right weapons, strategies, and knowledge.
Automating a manufacturing plant is to transition operation to a virtualized environment allowing operators to access a plant’s networks remotely and to gather data from machine controls and automation. The company finds the transition exciting and rewarding because the plant sees benefits in terms of efficiency and resources saved. But automation comes with potential threats, as many manufacturing companies have had their industrial networks attacked and usually don’t learn about it until significantly after the fact.
Using Best Practices is Essential
It is important to work with experienced automation systems integrators and to thoroughly familiarize management and staff with knowledge needed to thwart a wide variety of intrusions. The fact is that the fast-paced advancement of science and technology is putting manufacturing companies at the top of the target list because they have the most valuable information of interest to hackers. Today, cyber security is a Gordian Knot of issues for proliferating automation and control networks of which management cannot be ignorant.
Quick Pace of Change and New Platforms Complicate Security
Automation at many manufacturers means managing security and compliance across private, public, and hybrid cloud environments. Companies are interested in leveraging cloud computing because it saves money, but don’t want to give up anything in terms of security and compliance.
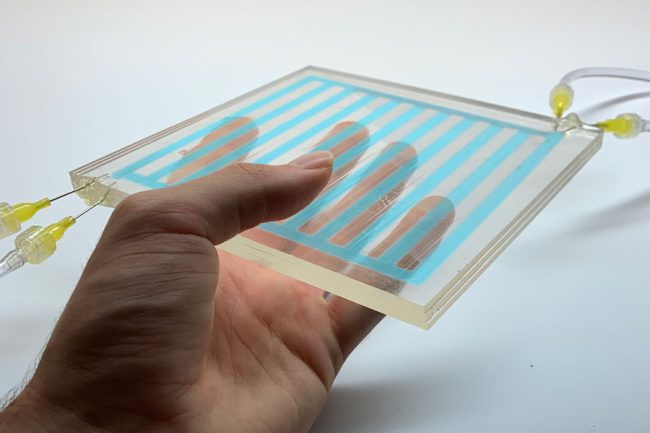
In a white paper “Exploiting Siemens Simatic S7 PLC” prepared for “Black Hat USA,” an annual industry security conference, and written by Dillon Beresford of NSS Labs, it is emphasized that many of today’s legacy protocols such as International Standards Organization Transport Service Access Point (ISO-TSAP RFC 1006) were designed without security in mind. Similarly, most Programmable Logic Controllers (PLCs) were built without any security in mind either. This has led to the deployment of insecure protocols in industrial control systems (ICS). As PLCs control critical processes in manufacturing plants, power plants, oil and gas drilling sites, and public transport control rooms, the need for a new generation of intrusion prevention systems is critical.
Related articles on IndustryTap:
- Cybershock: Terrorist Hackers Attacking Open Society
- “Major Cyber Attack” Costing Tens of Billions Expected by 2025
- Smart Grid Vulnerabilities & Protection From Cyber & Physical Attacks
References and related content: